Both involve hidden risks, weak links, and the cost of getting it wrong. Cybersecurity has become a board-level priority because of the staggering impact of a breach. Yet, equally complex and capable of inflicting financial and reputational damage, Customs compliance often remains overlooked until an audit strikes. Like cyber, Customs is largely invisible when everything runs smoothly, but a single vulnerability can trigger penalties, disrupt supply chains, and tarnish reputations.
This article explores how Customs can learn from the strategies that have made cybersecurity more resilient. From continuous monitoring to crisis planning, these five lessons show how businesses can move from reactive fire-fighting to proactive risk management.
Invisible Until Breached
No one notices cybersecurity until it fails. The same is true of Customs.
Both functions involve complex, often invisible systems. Both carry high-impact risks that are easy to underestimate until it’s too late. And in both cases, the cost of failure, whether it’s a data breach or a customs audit, can be reputational, financial, and operational.
Like cybersecurity, customs compliance operates quietly in the background until an error, investigation, or duty dispute brings it sharply into view. And just like a weak password or a missed patch, the most serious vulnerabilities often go unnoticed until they’re exploited.
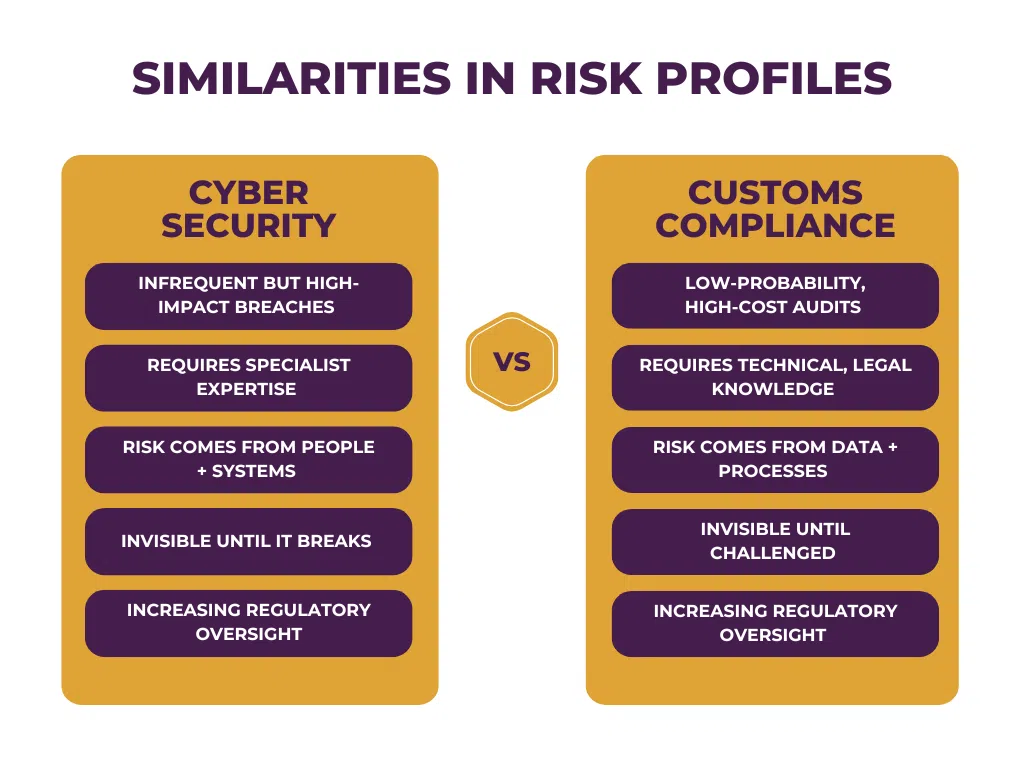
Both functions suffer from:
- Underinvestment (seen as cost centres, not value creators).
- Low visibility at board level – until an incident.
- Reliance on third parties (IT vendors/customs brokers).
- Human error and poor controls are the root cause of most failures.
In both cases, governance lags behind complexity. Most businesses don’t have dedicated Customs governance, audit trails, or escalation pathways – just as many didn’t have a CISO or incident plan a decade ago.
Five Lessons Customs Can Borrow From Cybersecurity
- Assume breach
Cybersecurity teams assume systems are always vulnerable. Customs functions should adopt a similar mindset: assume there are errors in the data and gaps in compliance, and proactively look for them. - Continuous monitoring
Cybersecurity uses real-time monitoring and penetration testing. Customs functions should regularly check entry data, broker performance, declaration accuracy, and classification quality, not just when an audit is looming. - C-Suite accountability
Most executive teams now receive regular cyber risk reporting. The same should be true of Customs. The financial, regulatory, and reputational stakes are simply too high to ignore. - Defence in depth
In cybersecurity, no single control is enough. In customs, relying on one broker, one internal process, or one spreadsheet creates fragility. Build resilience by layering oversight, tools, and expertise. - Crisis planning
Cybersecurity teams have breach playbooks. Customs teams should have audit response plans, voluntary disclosure procedures, and clear ownership of customs risk across the business.
Reframing Customs as a Strategic Risk
Cybersecurity has evolved from a back-office IT concern to a core board-level risk. Customs is heading in the same direction, especially in a post-Brexit environment where HMRC is increasingly data-led, and the risk of scrutiny is growing.
If your organisation wouldn’t dream of running without firewalls, penetration testing, or incident reporting, why accept Customs processes that haven’t been reviewed in a decade?
In cybersecurity, pen tests are designed to simulate attacks and reveal unseen weaknesses before they cause damage. CAT360 provides the same assurance for customs. By stress-testing declarations, classification, and origin, it uncovers errors, risks, and even reclaim opportunities before HMRC does.
Will You Be Ready?
The cost of getting it wrong in either case is rising. And as with cyber, the question isn’t whether you’ll be tested, it’s whether you’ll be ready when you are.
Contact Our Team …
Related Posts
27 April 2026
‘My Broker Told Me To Do It’: Why That Defence Won’t Save You At Tribunal
It is one of the most common things we…


